2000
|
The 6th day (2000)
Adam's blood analysis just before reading memory through the eyes, but this is not for identification.
Adam pays the taxi using his fingerprint.
|
 |
|
Adam Gibson's identity checked at the police station: "thumbprint checked against records...match confirmed".
|
 |
|
Adam steals Talia's car using her cut finger, lost after a gun shot.
|
 |
|
"Double X Charter" building fingerprint access control.
|
 |
|
Adam enters the WEIR building using Talia's cut finger.
|
 |
Talia is rejected because it's her second access.
Then security deactivates her credentials.
|
 |
|
And now the cut finger is of no use.
|
 |
|
So, back to the good old methods: Adam forces a guard to open doors with his fingerprint, twice.
|
 |
|
And a third time to access the computer (the guard is unconscious).
|
 |
Along Came a Spider (2000)
Fingerprint eraser machine: deposition of a kind of varnish on the skin.
|
 |
Antitrust (2000)
Dust for fingerprints on the computer keyboard.
|
 |
Followed by a manual match, using transparencies.
"Don't need a computer!" ;-)
|
 |
Charlie’s Angels (2000)
Eye reader of the security system protecting the computer of RedStar. Seems to be an iris system (very often confused with retinal scan).
|
 |
|
Stealing the iris image of the authorized person without cooperation.... Then a contact lens is made using the image.
|
 |
|
Contact lens used to fool the eye reader. Note it's only a colored lens... that's not a copy!
|
 |
|
Latent fingerprints are stolen on a beer bottle. Girls are lucky to get such a good print!
|
 |
|
Automated latent print reader. Note that the full hand is acquired: very lucky!
|
 |
|
Fake fingerprint maker: nice tool ;-)
|
 |
|
Fake fingerprints fool the "gelatin" reader.
|
 |
|
Knox has designed a voice-identification software which, combined with the GPS of RedStar, enables to localize Charlie.
|
 |
Dracula 2000 (2000)
The burglars break the security system that protects the crypt. After the password level, there is a palmprint security system...
|
 |
|
...spoofed with a latex fake.
|
 |
|
The voice recognition system is faked with a tape player.
|
 |
|
A fake electronic iris.
|
 |
|
Note that the pupil dilates!
|
 |
|
The electronic iris fakes the eye sensor.
|
 |
Hollow Man (2000) / L'homme sans ombre
Fingerprint recognition to access the lab.
|
 |
|
|
 |
|
Elevator to the lab with voice+speech recognition: Dr Caine deleted the access rights of his collegues to lock them in the lab.
|
 |
Mission Impossible 2 (2000)
Retinal scan to read the mission using the glasses.
|
 |
|
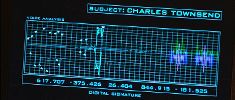
Facial recognition to identify John McCloy
|
 |
|
Vocal identification faked using a record.
|
 |
Mission to Mars (2000)
In a spaceship, millions of km from Earth, with only four people, the computer still needs a voice-print authentication system. Moreover, when authenticating, pressure is quickly dropping, which should slightly change the voice...
|
 |
X-Men (2000)
Prof. X eye scan ...
|
 |
|
... to access Cerebro.
|
 |
|
Later faked by Mystic...
|
 |
|
... who is able to impersonate anyone!
|
 |
Frequency (2000)
In 1969, Frank manages to grab some fingerprints of killer,
and sticks the fingerprint evidence in a bag. Then in 1999, John
can retrieve it and use modern technology to find out who the killer is.
|
 |
|




Biometrics visitors